Unfortunately, I get the same error.
i guess kernel 4.4 is missing anything in official image or libnl is too old
gunzip < /proc/config.gz | grep BRIDGE
this is how it looks like on 4.20:
root@bpi-r2:~# modprobe configs
root@bpi-r2:~# zgrep BRIDGE /proc/config.gz
# CONFIG_ARCH_FOOTBRIDGE is not set
CONFIG_BRIDGE_NETFILTER=m
CONFIG_NETFILTER_FAMILY_BRIDGE=y
# CONFIG_BRIDGE_NF_EBTABLES is not set
CONFIG_BRIDGE=m
CONFIG_BRIDGE_IGMP_SNOOPING=y
CONFIG_BRIDGE_VLAN_FILTERING=y
CONFIG_DRM_BRIDGE=y
CONFIG_DRM_PANEL_BRIDGE=y
you can also try to find bridge-module this way…
root@bpi-r2:~# find /lib/modules/$(uname -r) -name '*bridge*.ko'
/lib/modules/4.20.0-rc7-bpi-r2-fbdev/kernel/net/bridge/bridge.ko
if it is there try to load it (modprobe bridge) or try a depmod -a
you could try my image but have to bridge lanx/wan-ports instead of eth0/1 because of kernel 4.14
Ah okay. I found nothing like you have posted on my system.
afair bpi-team missed some modules in their official images…
shows module should be included…you can rebuild kernel and copy modules to its place…
i have only newer versions of my fork here compiled…
fastest way should be using one my images
Where can i find your images?
I need a simple debian to sniff the traffic.
Thanks to the great help from frank-w everything was configured so far. I have now created a bridge between the LAN port 1 & port 2, so that the clients in the LAN are routed through the bridge and vice versa. Now the tcpdump is missing. LAN1 goes to the firewall. LAN2 to the client network. if I put a tcpdump on LAN1, I get the info of the PI’s. However I need the information of the network of LAN2. Someone an idea?
Do you mean you want to monitor port 1 and 2? if yes, you can use “tcpdump -i br0 -xxx”, thanks.
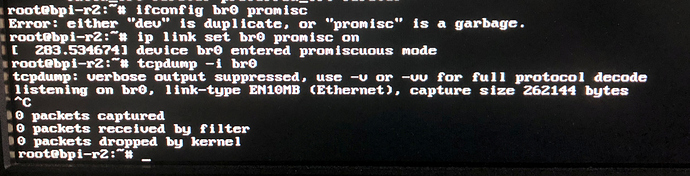
Yes. I need to monitor the traffic which goes through the bridge. Unfortunately, your command works not.
Any other idea?
Dsa-ports seem not supporting promiscuous mode…only traffic targeting r2 can be captured…all other (going through br0) are not shown
Unfortunately, it still does not work work.
It can not be that hard to create a dump. I just tested it with a server. Works (as expected) wonderful.
I guess its only a “setting” missing in dsa-driver
maybe it’s only a flag that needs to br handled…
Okay. So what have i to do now? ^^
@Ryder.Lee @moore can you help here getting promiscuous mode working on dsa-ports?
i see some messages in my bootlogs
[ 12.431431] device lan1 entered promiscuous mode
[ 12.431439] device eth0 entered promiscuous mode
[ 12.689326] device lan2 entered promiscuous mode
but i guess it is not really set in switch (mt7530)
Did you tey to use below command to enable promiscuous mode?
#ifconfig br0 promisc #ip link set br0 promisc on
imho tcpdump always try to set the device which listens on automaticly to promiscuous mode (except if -p is set). i guess mode is set in software, but not set in hardware, because it is not handled in driver (mt7530.c)
is it right to set promiscuous mode to br0 and not to the incoming dsa-port? i only used this for catching hw-ports but not in combination with sw-bridges.
Someone an idea? I need this as soon as possible …
https://lore.kernel.org/patchwork/patch/983190/
I guess that it causes the issue
So change to the latest user-land tools